Access control basics
Where IAM controls access
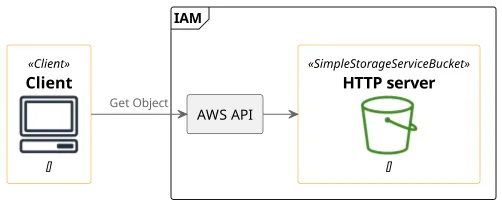
IAM controls access to AWS APIs only. While this is a broad surface, it does not contain everything.
Writing an object to an S3 bucket is done through the API. Similarly, creating new buckets, changing the metadata of existing objects, and setting up bucket replication are all done through the API and thus protected by IAM.
Apart from S3, invoking Lambda functions, starting EC2 instances, getting a list of IAM users in the account are all done through their respective APIs.
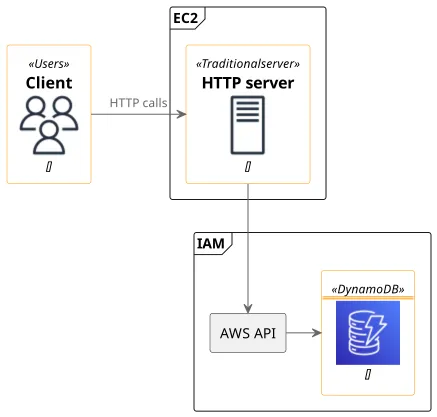
But if you have an EC2 instance with an Elastic IP hosting a webserver, calls to that server do not touch any AWS-provided APIs and thus they are not subjected to IAM policies. But when the webserver makes a request to DynamoDB to read an object, it goes to an AWS API again.
This might seem a limited scope, but AWS APIs are the gateways to almost everything happening inside the account. Every resource that is inside AWS is accessible only via the API. If you want to change anything, you need to use an API and that is subject to IAM.
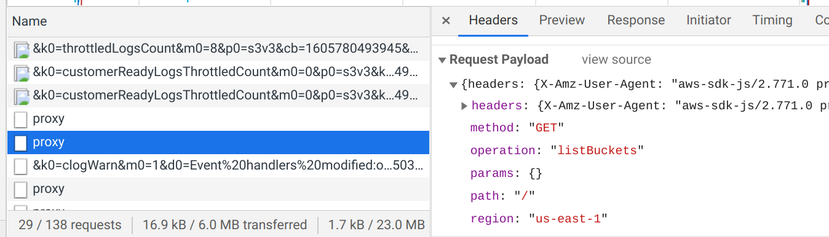
The Console and the SDKs all use the AWS API. This means (almost) everything you can do on the Console is subject to IAM policies. And that covers most of the things you do in an account.
That's why IAM is the most important security tool you have.
IAM protects AWS APIs only.